Documentation readiness and audit defensibility.
Harbor helps PPEC centers organize documentation completeness, maintain QA workflows, prepare for surveys and audits, and trace evidence back to the operating record — with security controls built for regulated healthcare.
Required artifacts stay organized and tracked.
Harbor tracks required artifacts — Plan of Care, orders, logs, incident reports, supporting documents — as structured records tied to payer, child, and time window. Gaps and expiring documents surface as owned work items before they become problems.
- Plan of Care lifecycle and versioning
- Orders and certifications tracked with expiry
- Transportation and attendance logs captured as evidence
- Incident reporting workflows and audit trails
Support billing evidence review before handoff.
Harbor helps QA teams surface documentation gaps before billing review — so the billing team is reviewing complete work, not cleaning up missing records. Teams trace evidence back to the child, day, authorization, and care documentation.
- Unified audit trail across modules
- Evidence packaging for billing support and audit reviews
- Owned work items with due dates for documentation gaps
When questions arise, trace the chain from billing evidence → care documentation → child record.
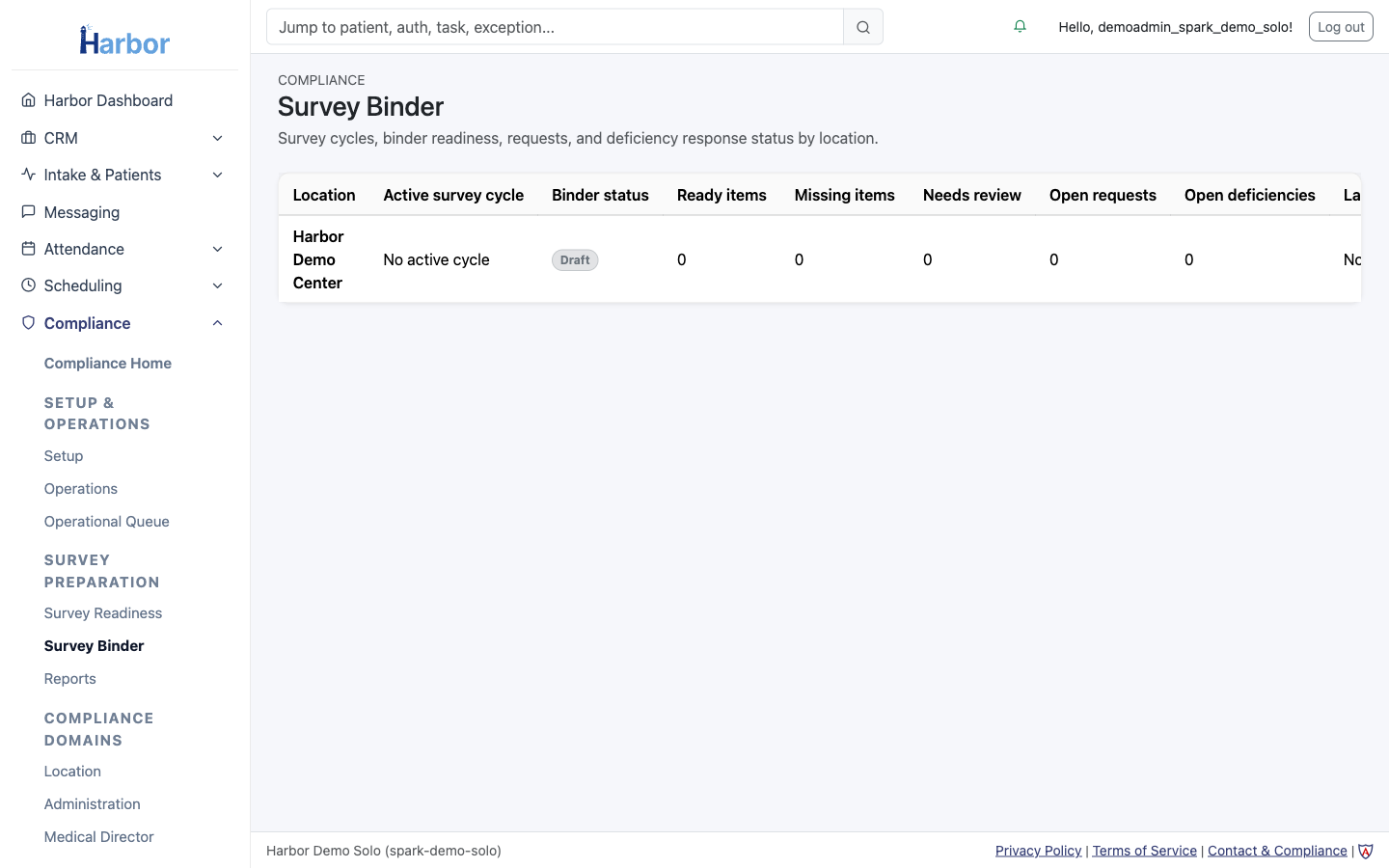
Survey binder — organized, not assembled at the last minute.
Harbor helps organize the documentation that surveyors and auditors ask for — so the center can respond quickly and defensibly. Survey readiness is not a separate project; it is the natural result of a well-maintained operating record.
- Survey binder organization and evidence packaging
- Audit defensibility through traceable, complete records
- Readiness status visible before surveys happen
Healthcare-grade protection.
Harbor is designed for regulated healthcare operations with controls that support HIPAA-aligned workflows. Security is layered across identity, data, infrastructure, and auditability.
Control highlights
- Role-based access control (least privilege)
- Tenant isolation for multi-center operations
- Encryption in transit and at rest
- Auditing and immutable event history for critical actions
- Secure integrations with monitoring and reconciliation
If you need a security overview for procurement, request a readiness review and we'll provide the security brief.
Have compliance questions?
We'll walk you through how Harbor handles documentation requirements, QA workflows, and security controls.